This is an opinion editorial by Joseph Totec, Treasure Brand Ambassador of SatoshiLabs.
Whether you’re considering buying your first hardware bitcoin wallet or have already had one for years, it’s always a good idea to refresh on the basics of these amazing tools. Contrary to popular belief, a hardware wallet is not a “set it and forget it” tool that will take care of your bitcoins for you. Instead, a hardware wallet can help you with your ongoing bitcoin security.
When and why should I buy a hardware wallet?
Since hardware wallets start at around $70, it’s clearly not a tempting idea to buy if you’re just dipping your toes into bitcoin. There is no clear cut-off point beyond which it is imperative that you buy a hardware wallet for yourself, but a good rule of thumb is to get it when you have around $1,000 worth of bitcoins to protect. When you stack regularly and bitcoin appreciates in the meantime, chances are you will quickly cross the $1,000 threshold, so don’t hold it for too long.
Some people believe that hardware wallets are unnecessary and an old phone/laptop will work perfectly in their place. The problem with such general-purpose devices is that virtually anything can run on such hardware and unless you’re an advanced security expert, you won’t know if a device is truly secure, even when connected to the Internet. Be disconnected (and honestly, security experts would agree that it’s not secure in the first place). Hardware wallets are special-purpose devices with firmware that performs a limited set of processes, namely generating keys and cryptographically signing them with those keys – all in a strictly offline environment.
Writing and Preserving Your Recovery Seed
When you’re setting up your hardware wallet, one of the first things the wallet does for you is that it generates your private key. To ensure that you will keep a hold of your bitcoin even if the particular device is lost or broken, you will be prompted to write your recovery seed: a human-readable secret that can be used to store your private key in other compatible wallets. can be done to recover.
Writing the 12 or 24 words that make up the recovery seed is one of the most important things you can do to protect your bitcoins. Hardware wallets usually don’t show a recovery seed – you need to write to it and keep it safe during the setup process.
Here are some basic tips for protecting your seed:
- write the words by hand on a piece of paper
- Alternatively, you can use a stronger solution such as Cryptosteel capsules or another metal solution.
- Never take a photo or keep a digital copy of the seed – hackers are actively looking for such data
- Store your recovery seed in a controlled access location away from water, fire hazard, etc.
- Consider Installing Shamir Backup — Multiple Recovery Seed Shares That Increase the Security of Your Seed
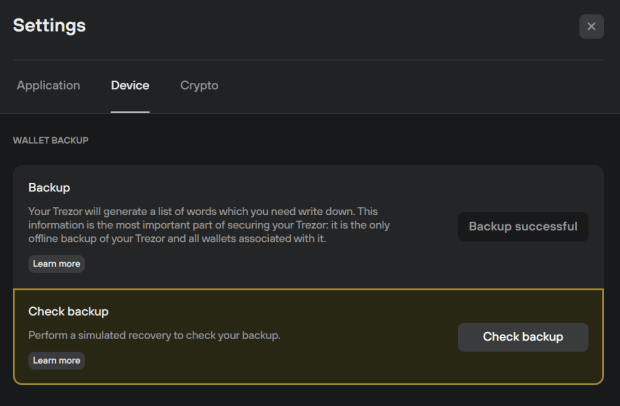
checking your recovery seed
Once you have written your recovery seed, it is advised to verify that it actually works to restore your wallet. You want to check the integrity of your seed before any bitcoins are attached, not after.
The best practice is to factory-reset your hardware wallet and then recover your wallet from seed. Alternatively, some hardware wallets offer dry-run recovery – this option will make you more comfortable if you already have some bitcoins stored on the device. For example, to perform a dry-run recovery in Trezor Suite, navigate to Settings, select “Check Backup” and follow the prompts (note that the connected Trezor device should respond in the third step – never seed words DO NOT INPUT IN THE COMPUTER. IF THE DEVICE DOES NOT RESPECT!)
It’s a good idea to check your seed backup regularly. If your security setup includes multiple Shamir backup shares, inspect them at least every 12 months to make sure the shares are still intact and ready for use when needed.
Setting up a PIN and Passphrase
Most hardware wallets can be secured with a PIN. A good PIN can prevent an attacker from stealing your funds when they discover your device, but note that a PIN only protects the device, not the recovery seed. So if the attacker were to discover both your device (protected by a PIN) and your recovery seed, they could steal all your bitcoins, as if they had a recovery seed in hand, they wouldn’t actually need the device. .
Fortunately, there is a way to reduce the risk of an attacker finding your recovery seed. Some hardware wallets, such as the Trezor device, provide the option to protect your seed with a passphrase. The passphrase helps you create a new set of wallets that are derived from the combination of a recovery seed and a special passphrase. This means that the seed itself becomes useless to an attacker, as they will not be able to obtain the correct set of wallets with the recovery seed alone.

Inputting the passphrase directly on the device eliminates the risk of the passphrase leaking to the keylogger.
If you’re having trouble telling the difference between a PIN and a passphrase, just remember: The PIN protects the device, the passphrase protects the seed.
If you choose to use a passphrase, don’t rely on your memory. If you forget the passphrase, there will be no way to access your funds. It is imperative that you back up your passphrase, just as you did for your seed. Keep the seed and passphrase separate and you’ll make it impossible for attackers to steal your money if you accidentally find one.
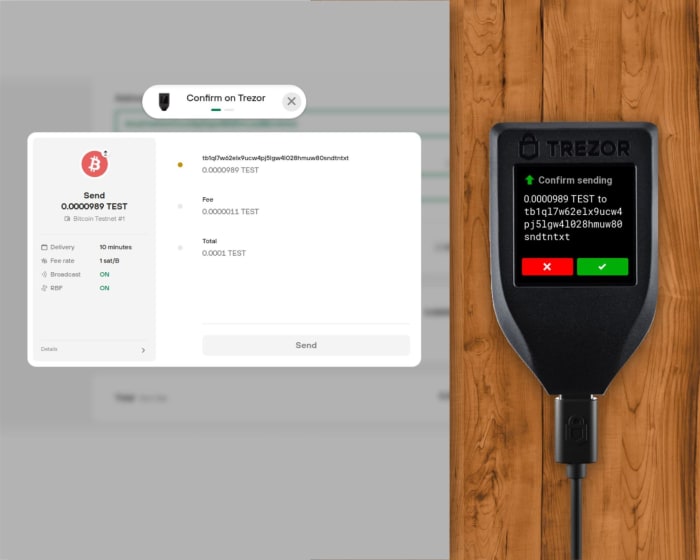
The device screen is there for a reason: Always verify your addresses!
Hardware wallets are useful beyond simple HODLing. One of the main advantages of these tools is the ability to receive and send bitcoins in a very secure manner.
A typical clipboard malware can change the address you are copying/pasting to your computer. If your computer is infected with such a virus, the only line of defense is to compare the address shown on the device to the sending/receiving counterparty (exchange website, your friend’s phone wallet, Signal message, etc.). This is one reason why all hardware wallets with their namesake must have their own screen, and why some cold storage solutions such as near-field communication (NFC) cards without screens are not good design choices.
When receiving bitcoins, the device will show the full address on its display, so you can independently verify that the address shown in the companion app is correct (ie, generated by the device). After verifying the address and giving it to your counterparty (either in the form of a scanned QR code or copy/pasted string), verify it again to make sure this clipboard was not modified by malware.
When sending bitcoins, the process involves several checks: verifying the address you’re sending, the associated fees, and the total amount. Be sure to double check everything!
Don’t rush into the process of verifying everything. Only the device screen can tell you exactly what’s going on inside the hardware wallet, so make sure you’re sending or receiving money exactly where you need it.
Beware the fishermen!
There are a lot of bad guys out there who would like to steal your bitcoins. Some choose to spread their nets through malware such as the one described above, while others try to take your coins through social engineering techniques – fake websites, e-mails or apps that try to make you type your seed. and passphrases are extensive.
The best defense is to remember one simple rule: Never type your seed into a website or app without hardware wallet guidance. When recovering your bitcoins with a hardware wallet like Trezor, you either type the seed words on the device (possible with the Trezor Model T), or the device tells you the order in which you need to type the words (eg. Treasure Model One), so that the correct sequence is not leaked to potential keyloggers or other spying techniques.
Routing via Tor, Connecting Your Full Node
To improve user privacy and prevent IP address leakage, it is recommended to route all bitcoin-related traffic through the Tor network. Tor is superior to a Virtual Private Network (VPN), as VPNs often keep logs of customer traffic that may be leaked or handed over to authorities when requested. With Tor, your IP address is virtually hidden, so your bitcoin transactions remain private (though keep in mind that if your bitcoin addresses are linked to yours then Tor itself will not protect you because you bought bitcoins on a centralized exchange that doesn’t. Knows your identity) You can route your bitcoin transactions originating from your hardware wallet with Bitcoin Core (see this guide) or other compatible wallet.
To further strengthen your privacy and sovereignty, you can connect your hardware wallet to a full node. When running your full node, you don’t need to rely on a third party to broadcast your transactions and give you the latest state of the bitcoin ledger. You can run a bitcoin full node on your home computer, laptop or Raspberry Pi device, and connect your hardware wallet via the bitcoin core HWI or Electrum.
Be prepared for real risks
The most common risk when handling bitcoin is accidental loss. Throwing out the recovery seed, sending or receiving money to the wrong address, falling for a phishing scam, forgetting the passphrase, or failing to detain yourself and later place the coins on a hacked exchange – it’s like no one else. There are many potential risk vectors in government seizure. The inconvenient truth is that Gitcoiners are their own worst enemy.
A good rule to remember is: test everything. After setting up your new hardware wallet, test that your recovery seed actually works, either by wiping the device or by dry run recovery. When you’re sending your first transaction using a hardware wallet, send the first few dollars to get a feel for how everything works. If it’s been a while since you’ve checked your seed, make sure it’s still there. If you are considering using a passphrase, try sending just a few sets to the new wallet and then try logging in and out a few times with and without the passphrase. If you ever find yourself in a stressful situation it will be to your advantage to become familiar with how hardware wallets should react.
Also note that all major hardware wallet manufacturers use a mutually-compatible recovery seed standard (BIP39 for regular seed or SLIP39 for Shamir Backup), so even if a particular manufacturer goes bankrupt, your coins will always be safe. And you should be able to recover your bitcoins in hardware of many open-source wallets, software.
This is a guest post by Joseph Tetek. The opinions expressed are solely their own and do not necessarily reflect those of BTC Inc. or Bitcoin Magazine.